A technical code fragment has been discovered on the New York Times website, revealing backend security and tracking mechanisms used by the publication. The code snippet contains various technical parameters including runtime configurations, client identification numbers, hash values, and security tokens. The fragment shows a variable declaration with multiple data points: a runtime type marked as 'c', a client ID string 'AHrlqAAAAAMAvAEsEb9w-s8AeVgFqA', and a hash value '499AE34129FA4E4FABC31582C3075D'. The code also includes a session size parameter of 17,439 bytes and references to geo-location captcha delivery systems hosted at 'geo.captcha-delivery.com'. Additionally, the fragment contains an encrypted security token and cookie data used for user session management and authentication purposes. This type of code is typically used by major news websites to manage user interactions, prevent automated access, and ensure secure content delivery. The presence of such technical elements highlights the complex infrastructure required to operate a major digital news platform like the New York Times, where security measures and user tracking systems work together to maintain site functionality and protect against unauthorized access.
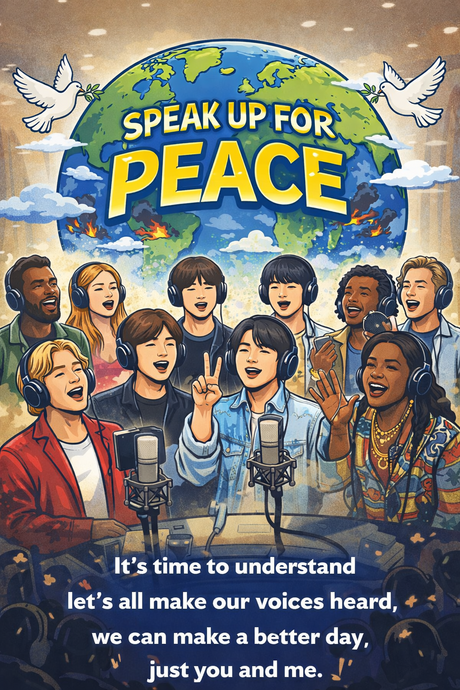
- A World at War, A Silence in Song: Why We Need a New “We Are the World”
- Seoul’s Spring Awakening: Step Into the City’s Galleries While the Moment Lasts
- Han Kang’s Latest Award Signals a Turning Point for Global Literature
- BTS Eyes Busan Stadium Shows in June as City Prepares for Tourism Surge
- When Global Icons Stay Silent: Why Artists Like BTS Matter in Times of War
- Monsta X Set for U.S. Comeback with New Album “Unfold”
- Damien Hirst’s First Major Asian Retrospective Opens in Seoul, Raising Questions Beyond Spectacle
- BTS Filled Gwanghwamun—and Moved the World. But It Stopped Short of Saying “Peace.”